Configure single sign-on for your organization using Microsoft Azure Active Directory.
First, you'll need to sign in to your Azure account. You can do so at https://azure.microsoft.com. If you don't yet have an Azure account, you can use this same URL to set one up.
Once you're logged in, click Portal, in the top right.
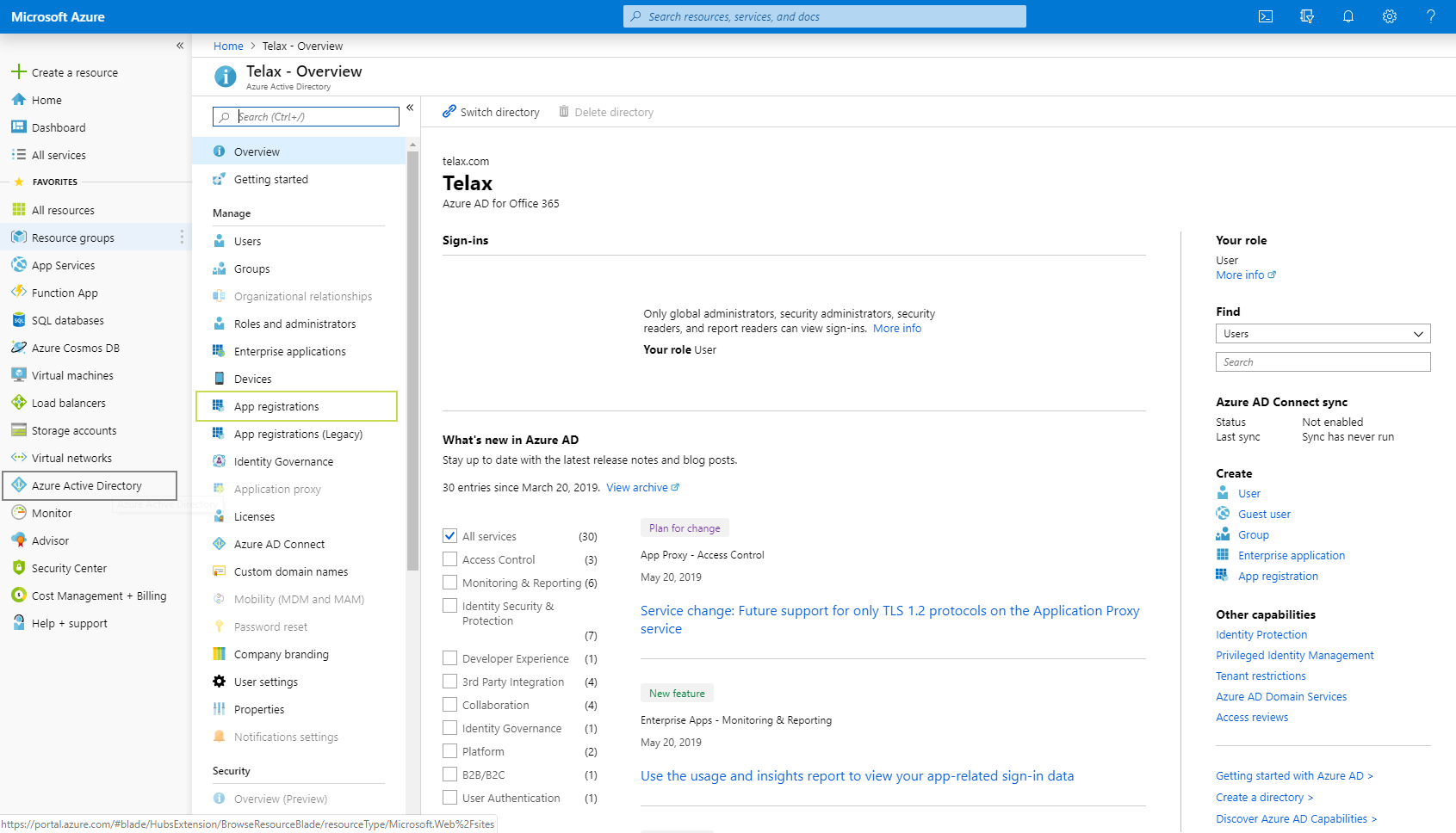
Now, from the navigation pane at left, click Azure Active Directory.
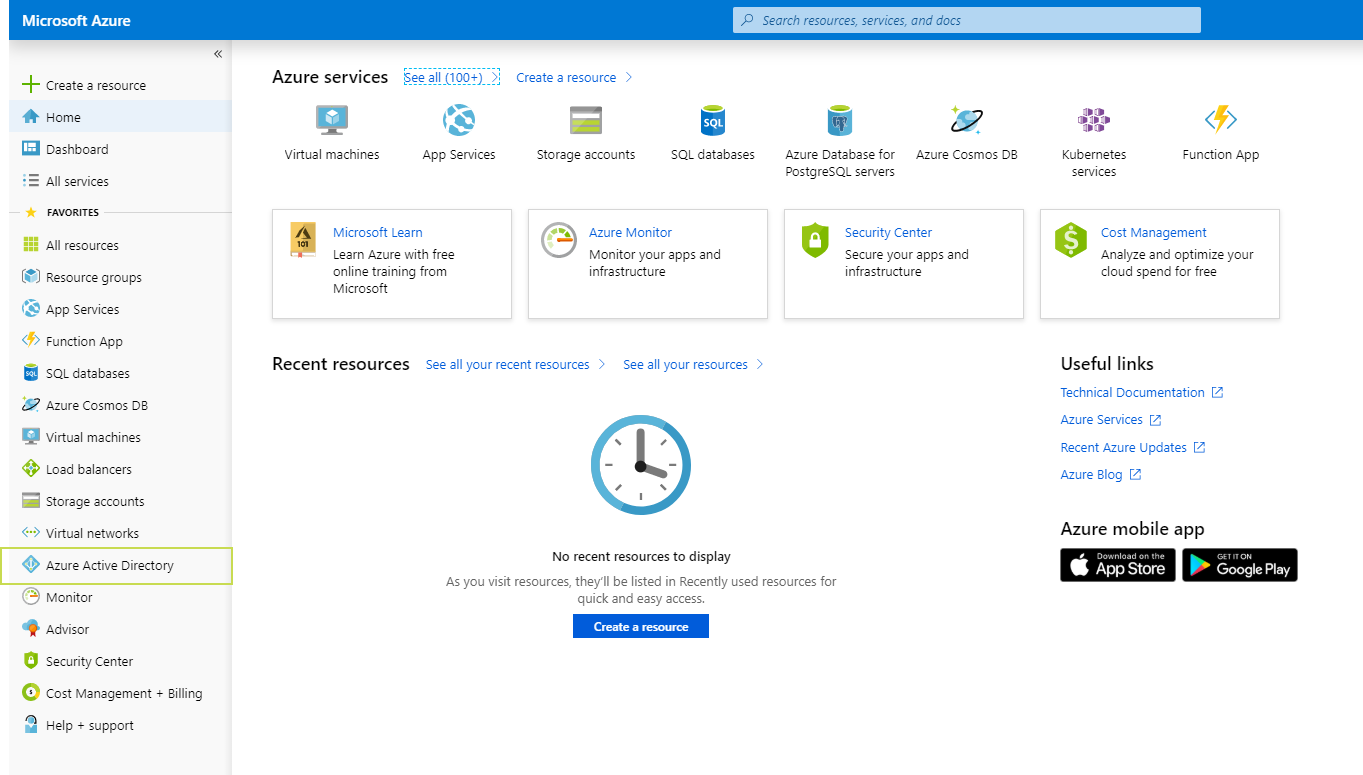
A secondary navigation pane will open - from there, click App Registrations (not "App Registrations (Legacy)").
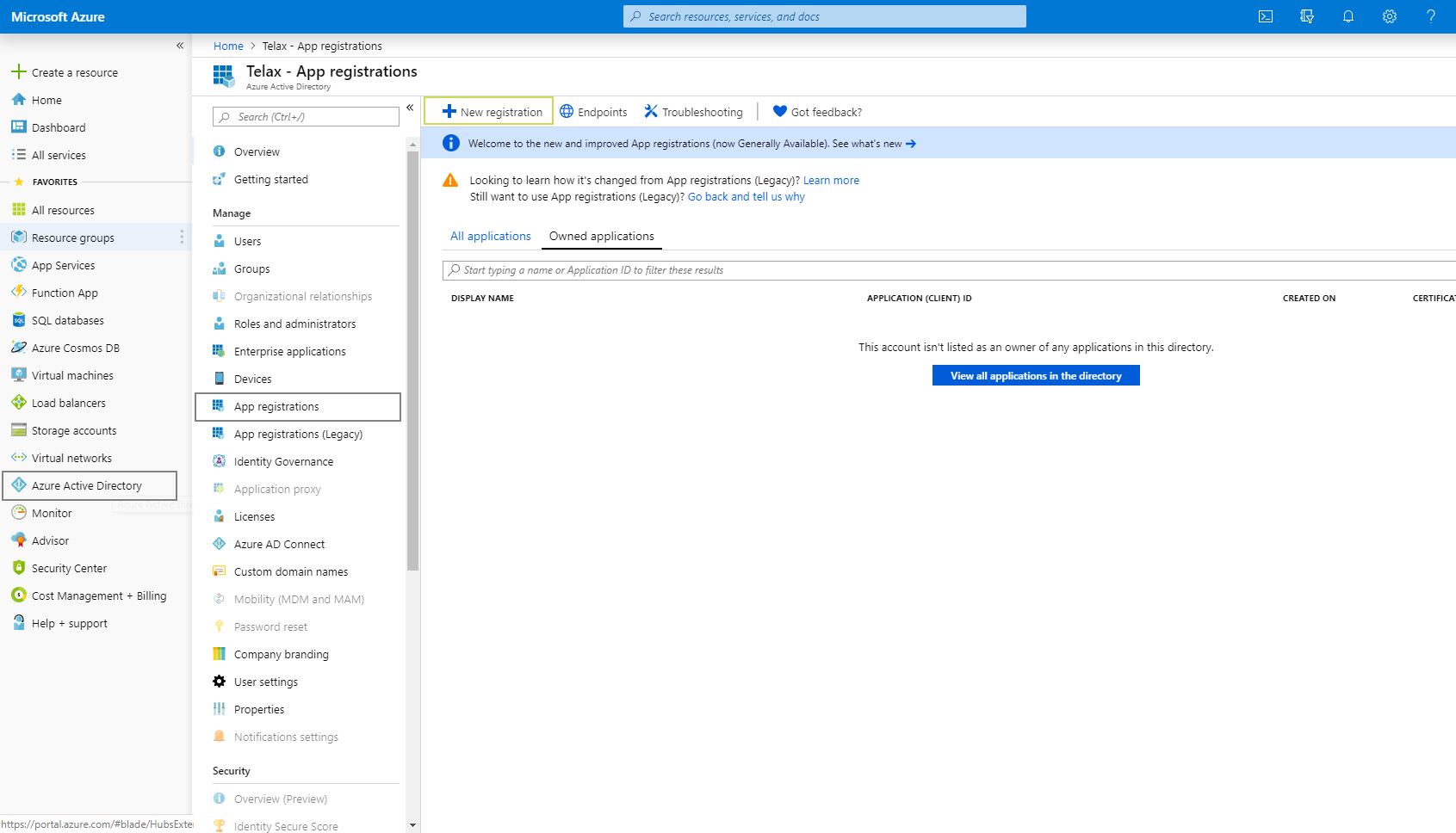
You'll see a third and final pane. From this one, click New Registration.
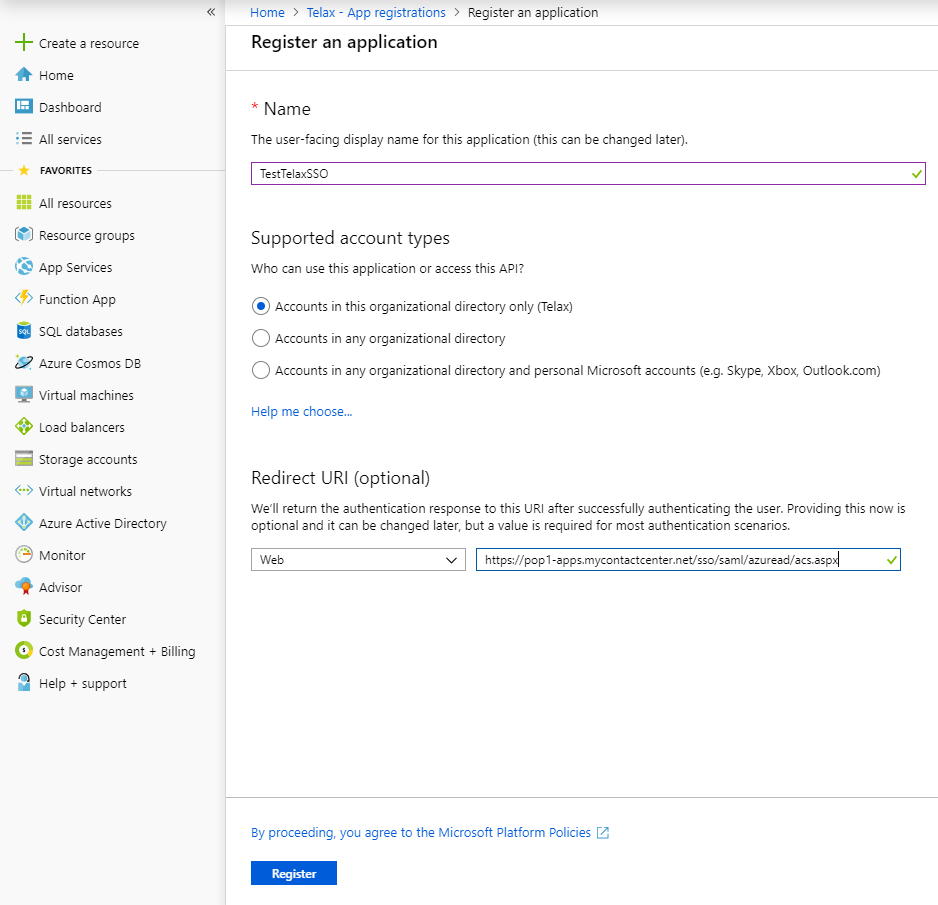
Please note that URI is required for SSO, although the Azure portal labels it as optional. |
Fill out all the information required to register an App:
https://pop0-apps.mycontactcenter.net/cca.sso/saml/azuread/acs.aspx (for web CCA)
https://pop1-apps.mycontactcenter.net/cca.sso/saml/azuread/acs.aspx (for web CCA)
When you're finished, click Register. Upon registration, the site will show the app's information, which should look something like the below.
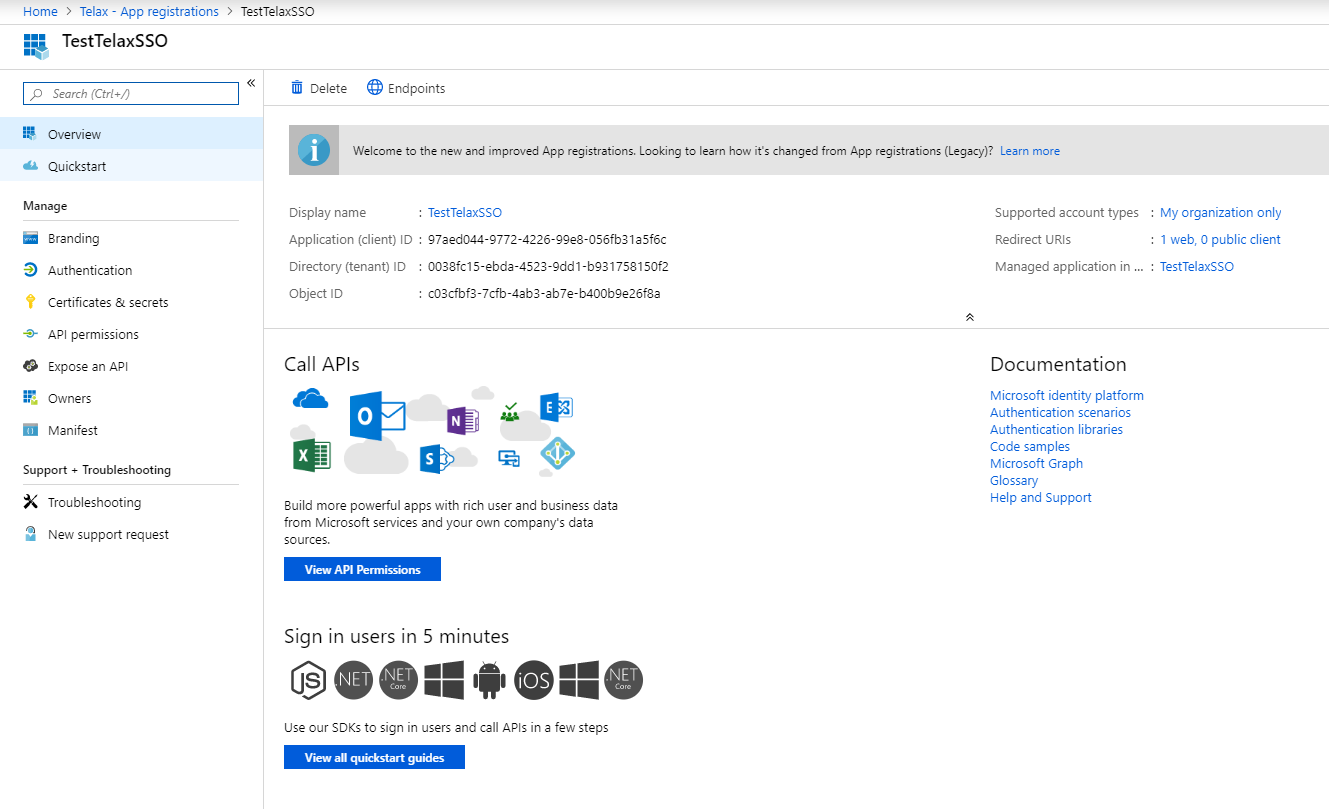
From this view, you can copy the Application (client) ID and the Directory (tenant) ID by simply hovering over them and clicking Copy to Clipboard.
There are some additional settings you'll need, so please continue through the steps below.
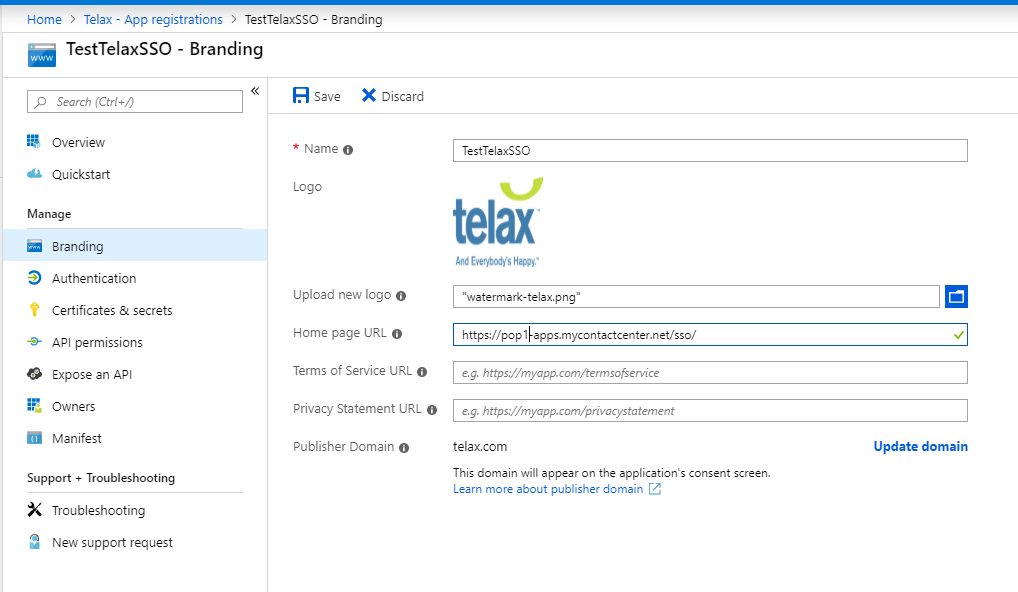
Under the Manage section, click Branding. Here you'll need to provide:
Remember to click on Save.
Now click Authentication. In this section, you'll need to provide:
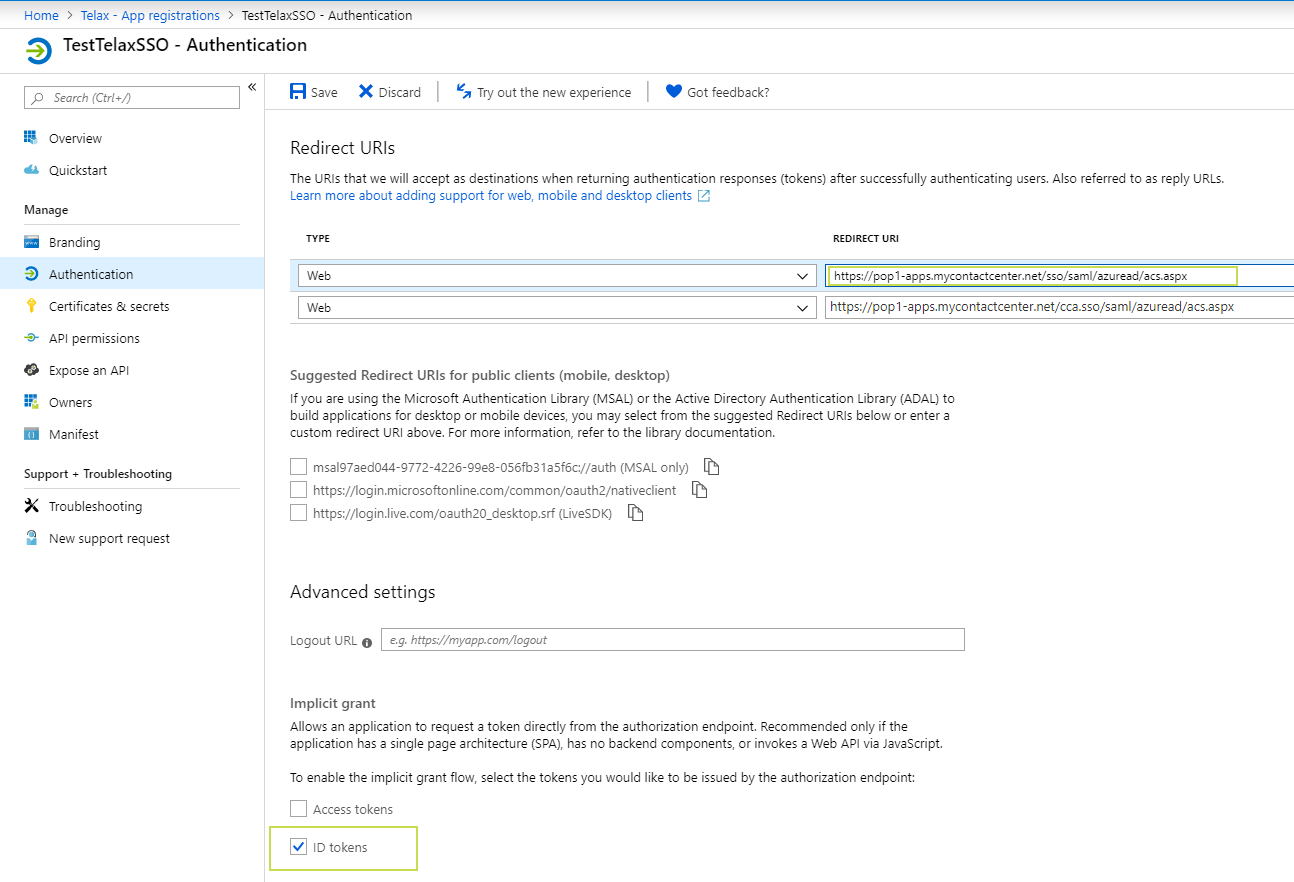
You may need to scroll down to see the options for Default client type and Supported account types.
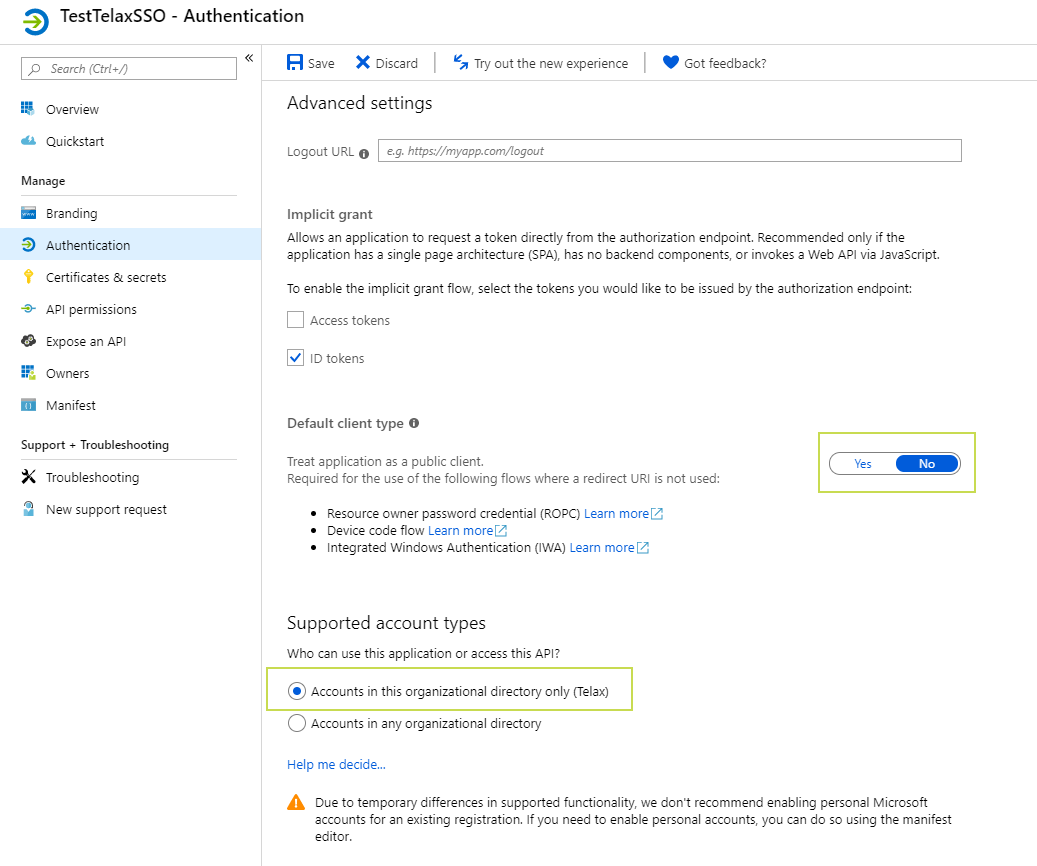
As before, be sure to click Save before proceeding.
It's not necessary to make changes here, but there is an optional setting you can change - see below.
As an administrator, you can grant consent on behalf of all users in this directory. Granting admin consent for all users means that end-users will not be shown a consent screen when using the application. |
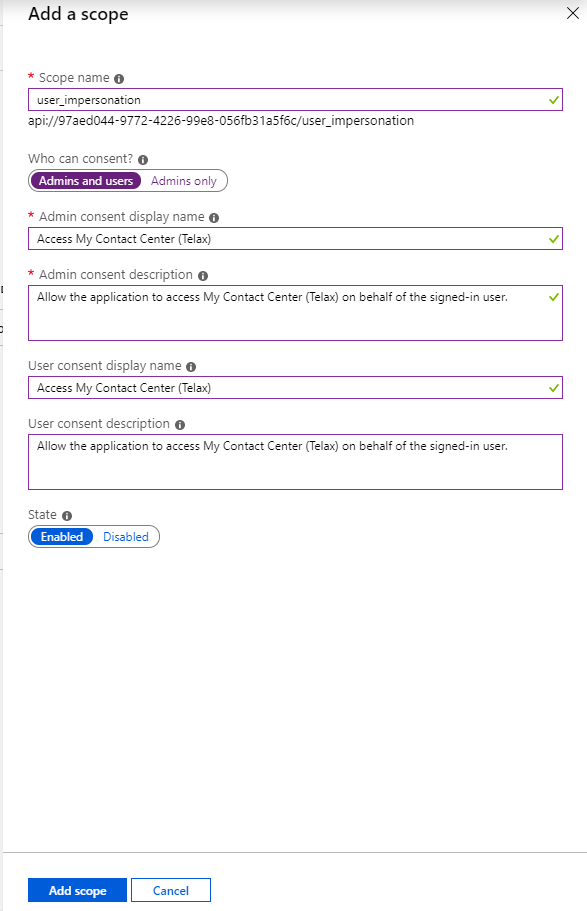
In this section, you're setting the scope that this API will cover.
Click the Add a scope button, and then provide the following info.
Scope name: user_impersonation
Who can consent? Select Admins and users
Admin consent display name: provide a name, such as "Access My Contact Center."
Admin consent description: enter a description, such as "Allow the application to access My Contact Center on behalf of the signed-in user."
User consent display name: provide a display name, such as "Access My Contact Center."
User consent description: enter a description, such as "Allow the application to access My Contact Center on behalf of the signed-in user.
State: Enabled.
Click on Add scope.
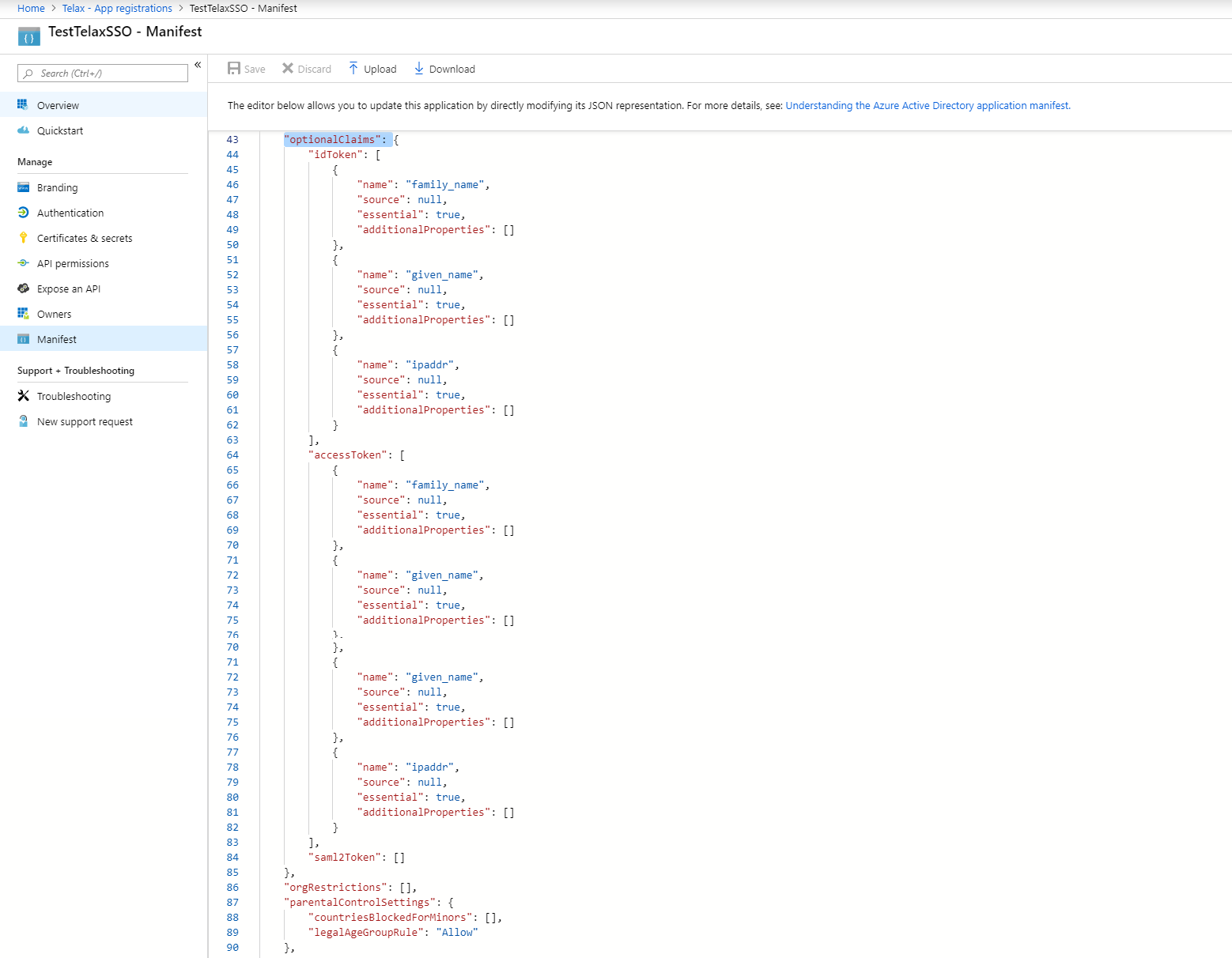
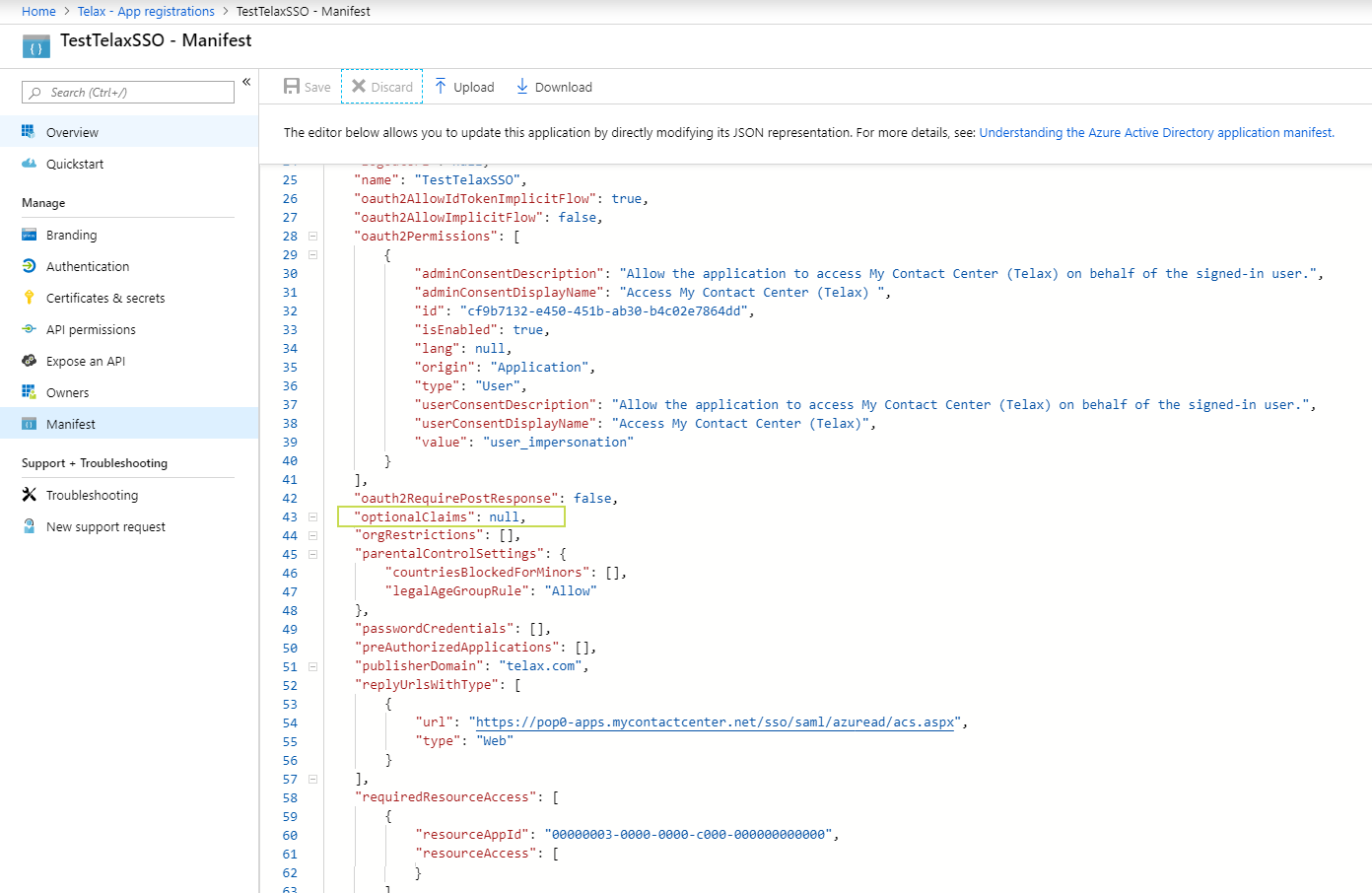
The manifest is the Application configuration file; here you can define or override various aspects of the application's configuration.
In this file manifest please replace the whole line containing:
"optionalClaims": null, |
with the following:
"optionalClaims": {
"idToken": [
{
"name": "family_name",
"source": null,
"essential": true,
"additionalProperties": []
},
{
"name": "given_name",
"source": null,
"essential": true,
"additionalProperties": []
},
{
"name": "ipaddr",
"source": null,
"essential": true,
"additionalProperties": []
}
],
"accessToken": [
{
"name": "family_name",
"source": null,
"essential": true,
"additionalProperties": []
},
{
"name": "given_name",
"source": null,
"essential": true,
"additionalProperties": []
},
{
"name": "ipaddr",
"source": null,
"essential": true,
"additionalProperties": []
}
],
"saml2Token": []
},
|
The below screenshot shows the location of this code (line 43). Scroll down for a screenshot showing the manifest after the changes.
Here is the manifest after making the above changes. Note that you may need to scroll to ensure all of the code has been pasted. After the change, the "optionalClaims": section should occupy 42 lines in total (in our example, from lines 43 through 85, inclusive).